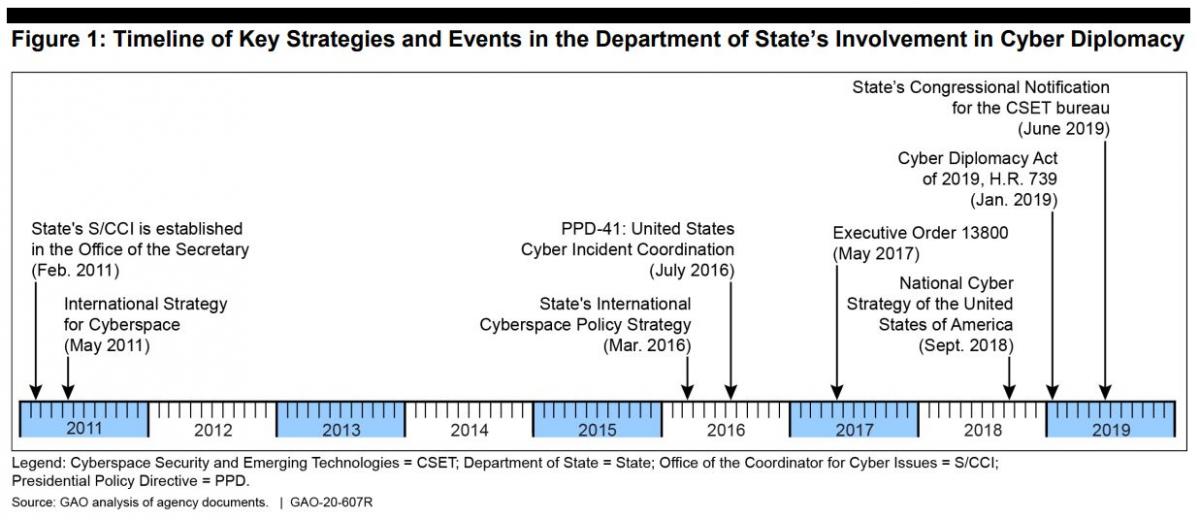
Following SolarWinds and Microsoft Exchange breaches, Congress considers its third cyber diplomacy bill since 2017
Previous administration demoted cyber diplomacy in favor of “defending forward” military strategy
GAO suggests new cyber bureau proposed by Pompeo days before Biden inauguration lacks data to achieve its intended goals