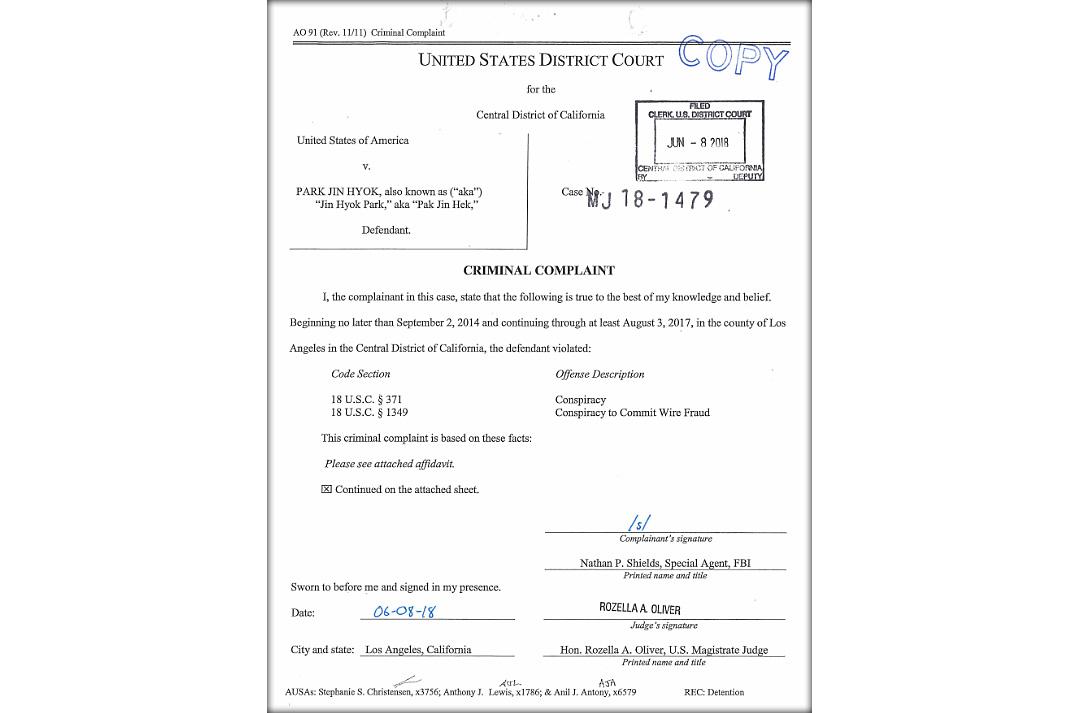
The United States Department of Justice today unsealed a criminal complaint (here) and arrest warrant for North Korean hacker Park Jin Hyok detailing his involvement in numerous cyber operations attributed to the Lazarus Group. Details in this document will likely advance the public’s understanding of how North Korea’s Reconnaissance General Bureau (RGB) conducts operations in cyberspace. In this posting the Cyber Vault presents a selection of documents intended to represent public understanding of the topic at the time of the criminal complaint’s release.
Documents
In this speech, Clapper uses an anecdote about a trip to North Korea to argue that a form of cyber deterrence would be appropriate for increasing the cost of North Korean cyber operations.
Kaspersky Lab, Lazarus Under the Hood, 2017. Not classified.
This report focuses on a group (Lazarus) whose cyber activities go back at least to 2009, and whose malware has been discovered in a number of serious cyber attacks (including the 2014 intrusion into the Sony Pictures computer system in 2014 and a 2013 cyber espionage campaign in South Korea). It reports on the results of the lab's forensic investigations in two geographically dispersed banks.
In their joint statement, the DNI, Under Secretary Defense for Intelligence, and the Director of NSA/Commander, U.S. Cyber Command discuss a variety of consequences of cyber threats - physical, commercial, psychological consequences - as cyber policy, diplomacy, and warfare. In addition, the statement discusses a number of cyber threat actors - nation states (Russia, China, North Korea, Iran), terrorists, and criminals - and responses to cyber threats.
In this letter to the Secretary of the Treasury, two members of Congress note recent reports that the Lazarus group, a hacking operation linked to the North Korean regime, had targeted banks in 18 different countries. In addition to providing more information about North Korean hacking activities, the authors request a briefing on Treasury Department interaction with private sector organizations to counter such activities.
This FBI report provides a summary and technical details with regard to the WannaCry ransomware campaign. It also recommends steps for prevention and remediation.
This alert - intended to help cyber defenders detect malicious cyber activity conducted by the North Korean government (designated HIDDEN COBRA) - contains indicators of compromise, malware descriptions, and network signatures.
This report surveys North Korea's cyber capabilities, offers potential motivations for North Korea's strategy, and examines four case studies.
This report examines the impact of WannaCry on the health sector of the United Kingdom, why the health sector was affected, and the effectiveness of the response.