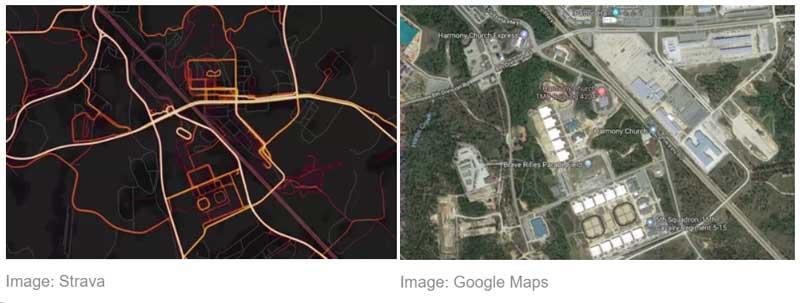
Today’s posting grows out of the recent spate of stories on the Strava heat map. Strava data unwittingly publicized highly precise location information on Western military bases and personnel around the world, including in some politically sensitive spots like the Middle East, and raised questions not just for the governments concerned but for private subscribers worried about protecting their own activities. Today’s items offer background on similar topics – namely security issues surrounding mobile devices and the Internet of Things.
New to the Cyber Vault

Department of Homeland Security
This report assesses the impact of multiple emerging technologies including advanced networking, quantum computing, autonomous learning, virtual/augmented reality, biometric identification and authentication, blockchain, and the impact of quantum computing on encryption
Related Documents from the Cyber Vault Library
This GAO technology assessment provides an introduction to the Internet of Things - describing what is known about current and emerging technologies and the implications of their use.
Department of Homeland Security, Study on Mobile Device Security, April 2017.
This study on mobile device security contains chapters on the mobile ecosystem; mobile security threats and defenses; mobile applications; threat prioritization, study findings, and gaps; recommendations for secure mobility in government; gaps in Department of Homeland Security authorities; and next steps.
This report was a response to tasking to examine the cybersecurity implications of the Internet of Things within the context of national security and emergency preparedness. Among the findings was that security factors to be considered with regard to the IoT were an "exponential expansion in attack surfaces, a changing threat landscape, privacy concerns, an increased potential for kinetic-focused cyber attacks, and changes to the hardware lifecycle."
This document focuses on the risks involved with the Internet of Things (the connection of systems and devices with primarily physical purposes to information networks, including the Internet) and provides a set of non-binding principles and suggests best practices to establish "a responsible level of security for the devices and systems businesses design, manufacture, own, and operate."
Federal Communications Commission, Cybersecurity Risk Reduction, January 18, 2017. Unclassified.
This report describes the twelve lines of effort undertaken by the FCC with regard to cybersecurity risk reduction - including those involving national security, public safety, real-time cyber threat information sharing, situational awareness, and international outreach.
This report explores vulnerabilities in the DoD from the "internet of things" and recommends a review of DoD policies and guidance to reflect the new category of threat.